ISACA Studying CyberSecurity
Fundamentals
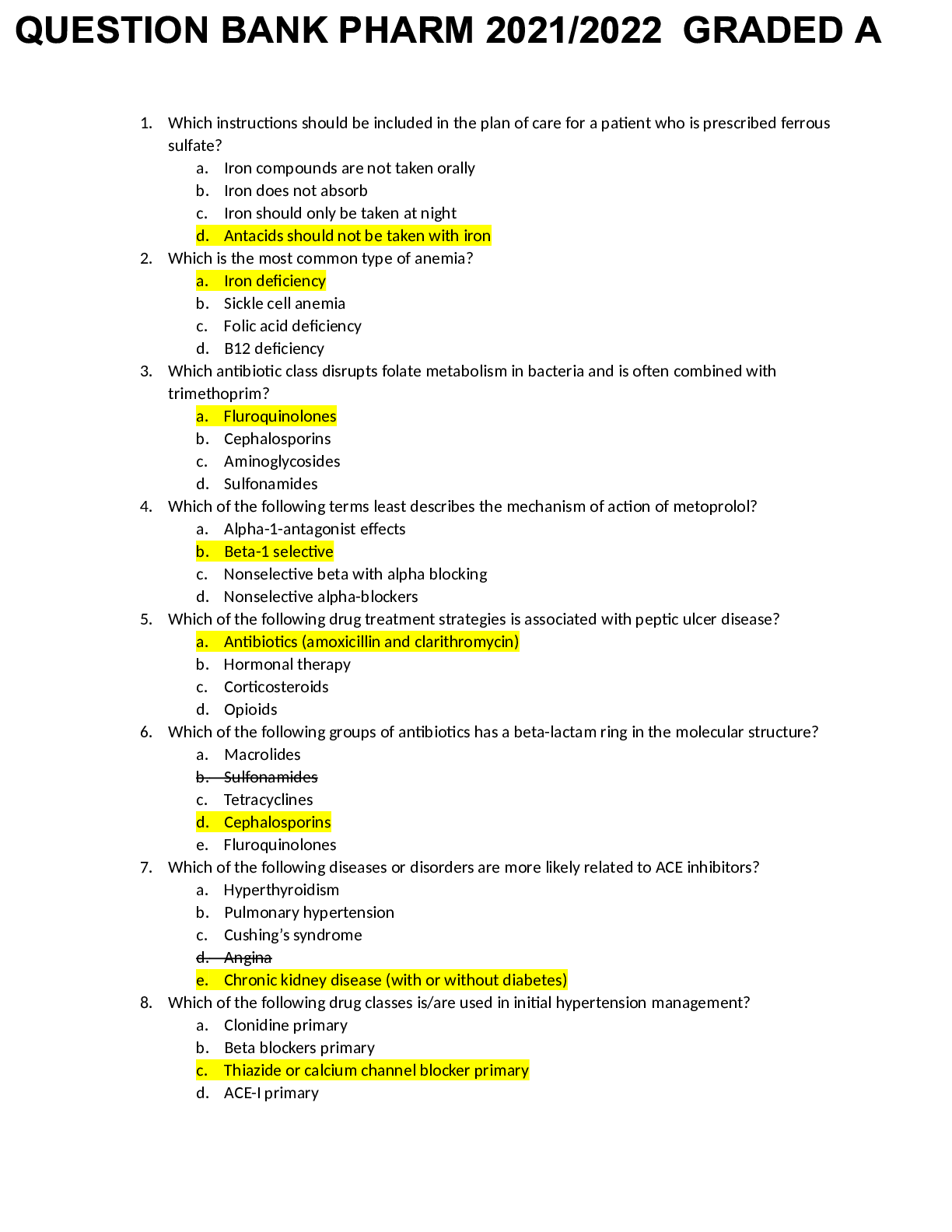
Three common controls used to protect availablity.
a) redundancy, backups and access control
b. Encryption, file permissions and access controls.
c. Access controls, logging
...
ISACA Studying CyberSecurity
Fundamentals
Three common controls used to protect availablity.
a) redundancy, backups and access control
b. Encryption, file permissions and access controls.
c. Access controls, logging and digital signatures.
d. Hashes, logging and backups. - ANS - A. Redundancy, backups and access control
Governance has several goals including:
a. providing strategic direction
b. ensuring that objectives are achieved
c. verifying that organizational resources are being used appropriately
d. directing and monitoring security activities.
e.Ascertaining whether risk is being managed properly - ANS - a. provisioning strategic
direction.
b. ensuring that objective are achieved
c. verifying that organizational resources are being used appropriately
e. Ascertaining whether risk is being managed properly.
Choose 3. According to the NIST framework which of the following are considered key
functions necessary for the protection of digital assets?
a. Encrypt b. Protect c. Investigate d. Recover e. Identify - ANS - B. Protect
D.recover
E. Identify
Which of the following is the best definition for cybersecurity?
a. The process by which an organization manages cybersecurity risk to an acceptable level
b. The protection of information from unauthorized access or disclosure
c. The protection of paper documents, digital and intellectual property, and verbal or visual
communications d. Protecting information assets by addressing threats to information that is
processed, stored or transported by interworked information systems - ANS - d. Protecting
information assets by addressing threats to information that is processed, stored or transported by
internetworked information systems.
Which of the following cybersecurity roles is charged with the duty of managing incidents and
remediation?
a. Board of directors
b. Executive committee
c. Cybersecurity management
d. Cybersecurity practitioner - ANS - c. Cybersecurity managment
The core duty of cybersecurity is to identify, respond and manage ________ to an organization's
digital assets. - ANS - Risk
A ________ is anything capable of acting against an asset in a manner that can cause harm. -
ANS - Threat
A _______ is something of value worth protecting. - ANS - Asset
A _________ is a weakness in the design, implementation, operation or internal controls in a
process that could be exploited to violate the system security - ANS - vulnerability
the path or route used to gain access to the target asset is known as a ______ - ANS - attack
vector
In an attack, the container that delivers the exploit to the target is called? - ANS - Payload
______ communicates required and prohibited activities and behaviors - ANS - Policies
_____ is a class of malware that hides the existence of other malware by modifying the
underlying operating system - ANS - Rootkit
_______ provides details on how to comply with policies and standards. - ANS - Procedures
______ contain step-by-step instructions to carry out procedures - ANS - Guidelines
________ also called malicious code, is software designed to gain access to targeted computer
systems. steal info or disrupt computer operations. - ANS - Malware
_________ are used to interpret policies in specific situations - ANS - Standards
____ are solutions to software programming and coding errors - ANS - Patches
_______ includes many components such as directory services, authentication and authorization
services, and user management capabilities such as provisioning and deprovisioning - ANS -
Identity Management
Select all that apply. The Internet perimeter should:
a. Detect and block traffic from infected internal end points.
b. Eliminate threats such as email spam, viruses and worms.
c. Format, encrypt and compress data.
d. Control user traffic bound toward the Internet.
e. Monitor and detect network ports for rogue activity. - ANS - A. detect and block traffic from
infected internal end points.
b. eliminate threats such as email spam, viruses and worms.
d. control user traffic bound towards the Internet,
e. monitor and detect network ports for rogue activity.
The __________________ layer of the OSI model ensures that data are transferred reliably in the
correct sequence, and the ________________ layer coordinates and manages user connections.
a. Presentation, data link
b. Transport, session
c. Physical, application
d. Data link, network - ANS - Transport and session
Choose three. There key benefits of the DMZ system are: a. DMZs are based on logical rather
than physical connections.
b. An intruder must penetrate three separate devices.
c. Private network addresses are not disclosed to the Internet.
d. Excellent performance and scalability as Internet usage grows.
e. Internal systems do not have direct access to the Internet. - ANS - b. An intruder must
penetrate three separate devices
c. Private network addresses are not disclosed to the Internet.
e. Internal systems do not have direct access to the internet
Which of the following best states the role of encryption within an overall cybersecurity
program?
a. Encryption is the primary means of securing digital assets.
b. Encryption depends upon shared secrets and is therefore an unreliable means of control.
c. A program's encryption elements should be handled by a third-party cryptologist.
d. Encryption is an essential but incomplete form of access control. - ANS - D.Encryption is an
essential but incomplete form of access control.
The number and types of layers needed for defense in depth are a function of:
a. Asset value, criticality, reliability of each control and degree of exposure.
b. Threat agents, governance, compliance and mobile device policy.
c. Network configuration, navigation controls, user interface and VPN traffic.
d. Isolation, segmentation, internal controls and external controls. - ANS - A. Asset value,
criticality, reliability of each control and degree of exposure.
Put the steps of the penetration testing phase into
[Show More]