Computer Networking > EXAM > Real 312-50v10 Certified Ethical Hacker Exam (C|EH v10) Test Questions V11.02 | Killtest (All)
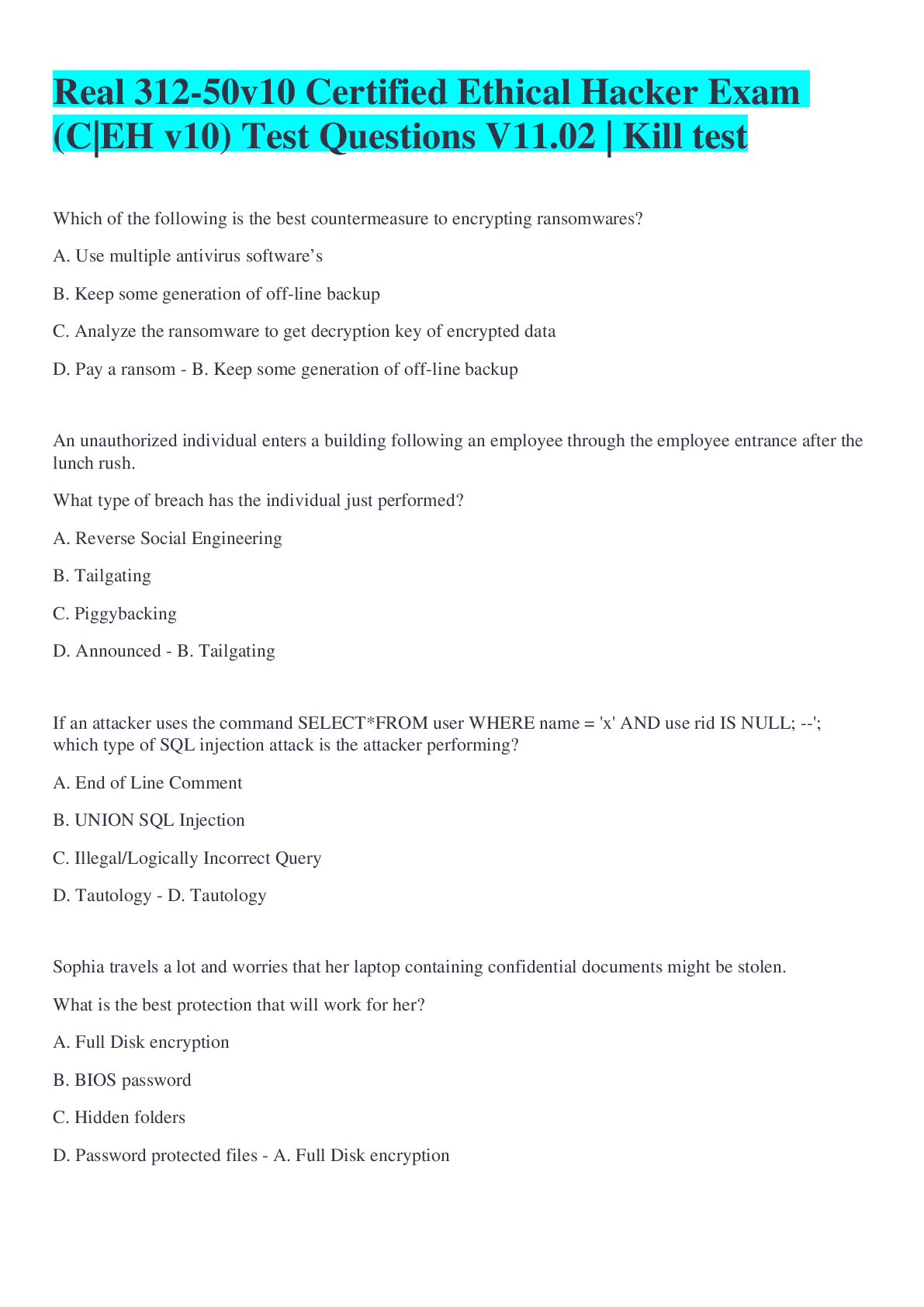
Real 312-50v10 Certified Ethical Hacker Exam (C|EH v10) Test Questions V11.02 | Killtest
Document Content and Description Below
Which of the following is the best countermeasure to encrypting ransomwares? A. Use multiple antivirus softwares B. Keep some generation of off-line backup C. Analyze the ransomware to get decrypti... on key of encrypted data D. Pay a ransom B. Keep some generation of off-line backup An unauthorized individual enters a building following an employee through the employee entrance after the lunch rush. What type of breach has the individual just performed? A. Reverse Social Engineering B. Tailgating C. Piggybacking D. Announced B. Tailgating If an attacker uses the command SELECT*FROM user WHERE name = 'x' AND userid IS NULL; --'; which type of SQL injection attack is the attacker performing? A. End of Line Comment B. UNION SQL Injection C. Illegal/Logically Incorrect Query D. Tautology D. Tautology Sophia travels a lot and worries that her laptop containing confidential documents might be stolen. What is the best protection that will work for her? A. Full Disk encryption B. BIOS password C. Hidden folders D. Password protected files A. Full Disk encryption An attacker has installed a RAT on a host. The attacker wants to ensure that when a user attempts to go to "www.MyPersonalBank.com", that the user is directed to a phishing site. Which file does the attacker need to modify? A. Boot.ini B. Sudoers C. Networks D. Hosts D. Hosts Which of the following options represents a conceptual characteristic of an anomaly-based IDS over a signature-based IDS? A. Produces less false positives B. Can identify unknown attacks C. Requires vendor updates for a new threat D. Cannot deal with encrypted network traffic B. Can identify unknown attacks You are logged in as a local admin on a Windows 7 system and you need to launch the Computer Management Console from command line. Which command would you use? A. c:\gpedit B. c:\compmgmt.msc C. c:\ncpa.cp D. c:\services.msc B. c:\compmgmt.msc Which of the following act requires employer's standard national numbers to identify them on standard transactions? A. SOX B. HIPAA C. DMCA D. PCI-DSS B. HIPAA In Wireshark, the packet bytes panes show the data of the current packet in which format? A. Decimal B. ASCII only C. Binary D. Hexadecimal D. Hexadecimal [Show More]
Last updated: 2 years ago
Preview 1 out of 5 pages
Buy this document to get the full access instantly
Instant Download Access after purchase
Buy NowInstant download
We Accept:

Reviews( 0 )
$10.00
Can't find what you want? Try our AI powered Search
Document information
Connected school, study & course
About the document
Uploaded On
Oct 28, 2022
Number of pages
5
Written in
Additional information
This document has been written for:
Uploaded
Oct 28, 2022
Downloads
0
Views
25