WGU C836 MULTI/COMPREHENSIVE
FINAL EXAM REVIEW (LATEST
VERSION 2022)
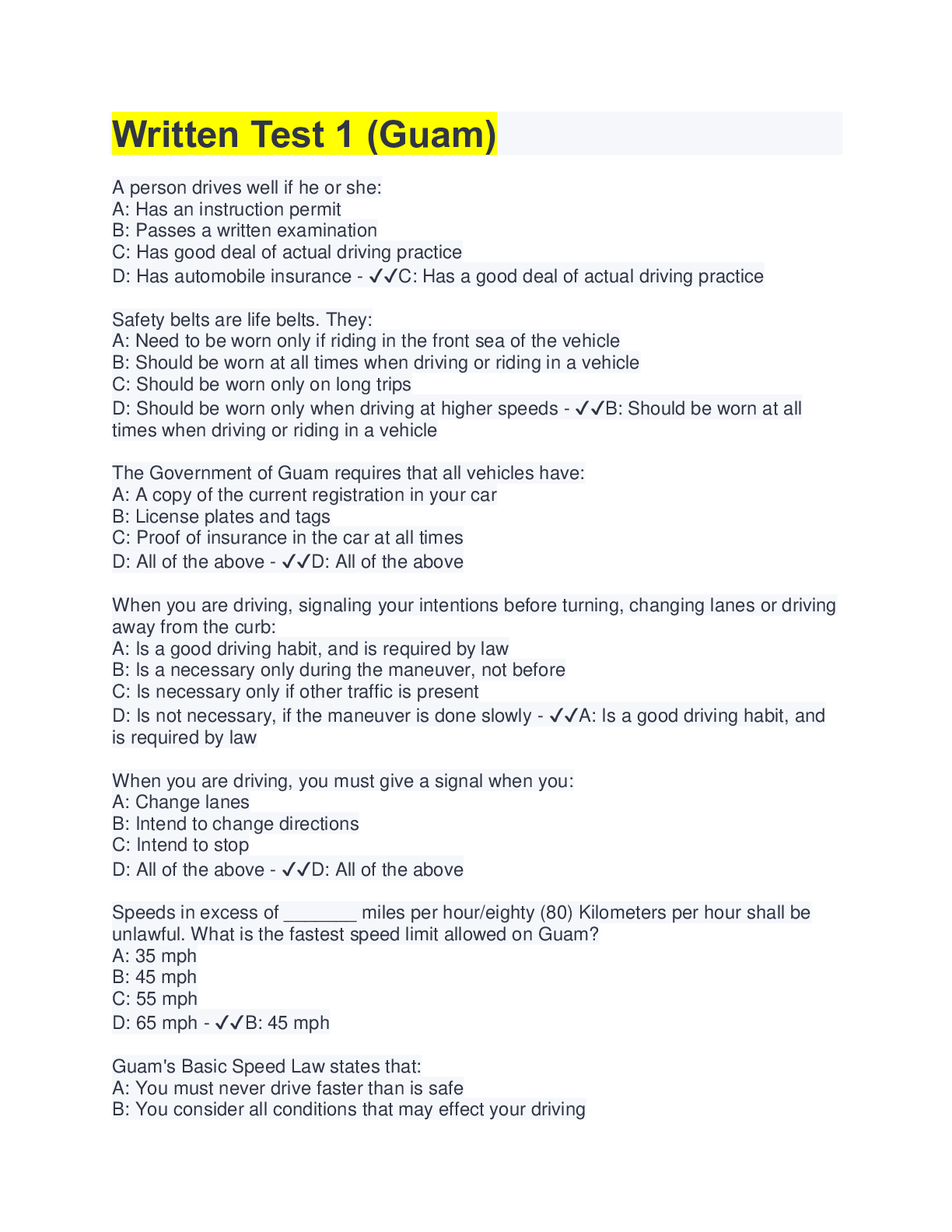
______ regulates the financial practice and governance of corporations. This task contains the
radio buttons and checkboxes for options. The shortc
...
WGU C836 MULTI/COMPREHENSIVE
FINAL EXAM REVIEW (LATEST
VERSION 2022)
______ regulates the financial practice and governance of corporations. This task contains the
radio buttons and checkboxes for options. The shortcut keys to perform this task are A to H and
alt+1 to alt+9.
A.GLBA
B.FISMA
C.SOX
D.FERPA
E.HIPAA Correct Answer- C.SOX
_______ provides us with the means to trace activities in our environment back to their source.
This task contains the radio buttons and checkboxes for options. The shortcut keys to perform
this task are A to H and alt+1 to alt+9.
A.Access
B.Authentication
C.Accountability
D.Authorization
E.Nonrepudiation Correct Answer- C.Accountability
_____________ is a popular, fully-featured sniffer capable of intercepting traffic from a wide
variety of wired and wireless sources.
A.Wireshark
B.Kismet
C.Hping3
D.NetStumbler Correct Answer- A.Wireshark
_____________ is a sniffer that specializes in detecting wireless devices.
A.Hping3
B.Kismet
C.Wireshark
D.NetStumbler Correct Answer- B.Kismet
A combination of a network design feature and a protective device such as a firewall; often
used for systems that need to be exposed to external networks but are connected to our
network (such as a web server) Correct Answer- Demilitarized Zone (DMZ)
A combination of DAC and MAC, primarily concerned with the confidentiality of the resource.
Two security properties define how information can flow to and from the resource: the simple
security property and the * property. Correct Answer- The Bell-LaPadula model
A database is vulnerable to SQL injection attacks through direct attempts to the database
server or through applications software, including web applications. What is the most effective
way of mitigating these attacks?
A.Authenticating the user on the client-side
B.Authenticating the user on the server-side
C.Keeping the software patched
D.Turning on database logging
E.Validating user inputs Correct Answer- E.Validating user inputs
A firewall technology that can analyze the actual content of the traffic that is flowing through
Correct Answer- Deep packet inspection
A firewall technology that functions on the same general principle as packet filtering firewalls,
but is able to keep track of the traffic at a granular level. Has the ability to watch the traffic over
a given connection Correct Answer- Stateful packet inspection
A firewall technology that inspects the contents of each packet in network traffic individually
and makes a gross determination (based on source and destination IP address, port number,
and the protocol being used) of whether the traffic should be allowed to pass Correct AnswerPacket filtering
A firewall that can watch packets and monitor the traffic from a given connection is using what
kind of firewall technology?
A.Deep packet inspection
B.Stateful packet inspection
C.Packet filtering Correct Answer- B.Stateful packet inspection
A fully featured sniffer that is also a great tool for troubleshooting traffic; this well-known tool
is used by many network operations and security teams Correct Answer- Wireshark
A group of tools that can include network mapping tools, sniffers, and exploits Correct AnswerExploit framework
A hardware- and software-based technology that prevents certain portions of the memory used
by the operating system and applications from being used to execute code Correct AnswerExecutable space protection
A model that adds three more principles to the CIA triad: possession or control, utility, and
authenticity Correct Answer- Parkerian hexad
A multilayered defense that will allow us to achieve a successful defense should one or more of
our defensive measures fail Correct Answer- Defense in depth
A particularly complex and impactful item of malware that targeted the Supervisory Control
and Data Acquisition (SCADA) systems that run various industrial processes; this piece of
malware raised the bar for malware from largely being a virtual-based attack to actually being
physically destructive Correct Answer- Stuxnet
A phrase that refers to an organization's strategy and policies regarding the use of personal vs.
corporate devices Correct Answer- Bring your own device (BYOD
A principle that states we should only allow a party the absolute minimum permission needed
for it to carry out its function Correct Answer- The principle of least privilege
A program that seeks to make users aware of the risk they are accepting through their current
actions and attempts to change their behavior through targeted efforts Correct AnswerSecurity Awareness, Training, and Education (SATE)
[Show More]
.png)


.png)




![Preview of [SOLVED] EDCO 740 / EDCO740 Quiz 1 (LATES 2021/2022 Graded A)](https://scholarfriends.com/storage/EDCO_740_Quiz_1.png)