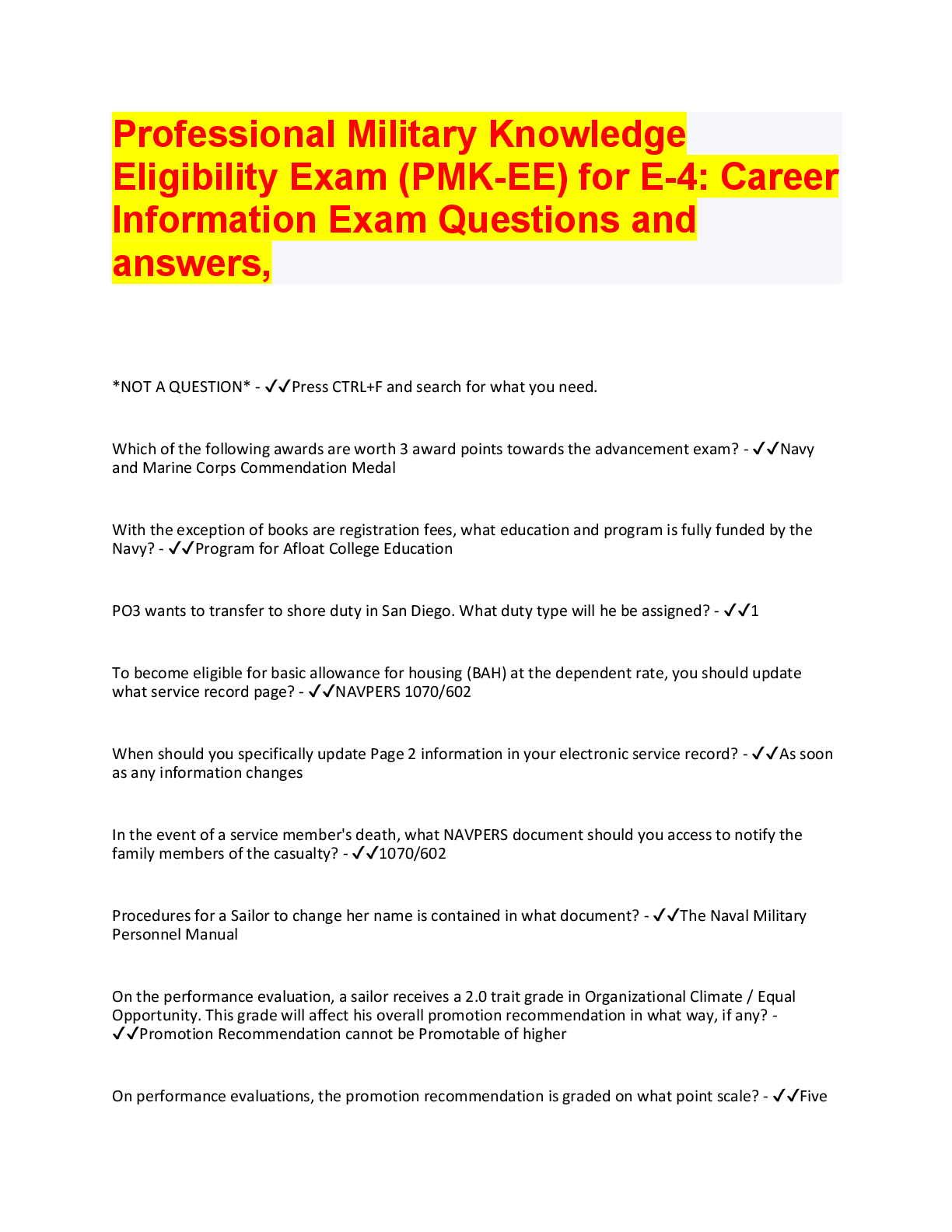
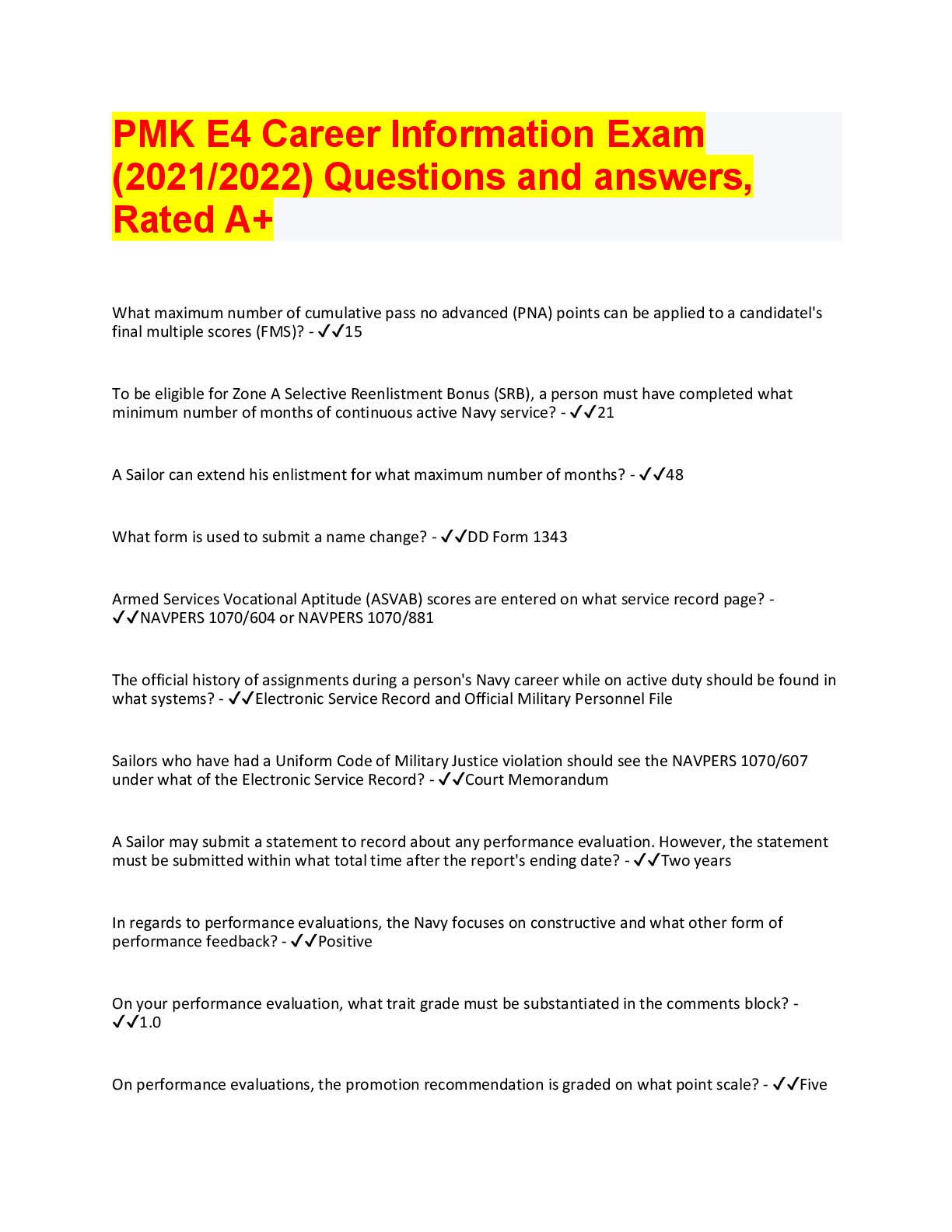
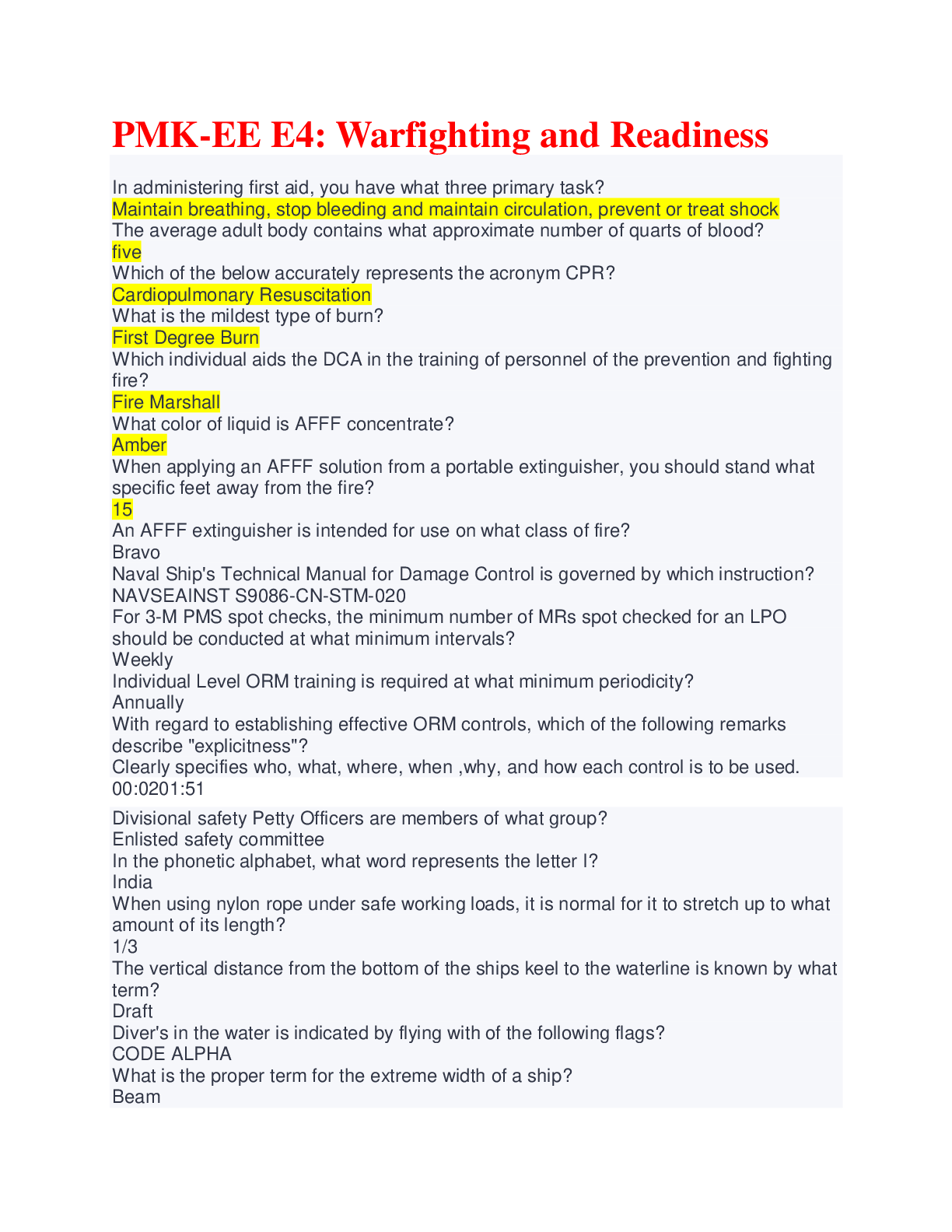
CCSP - Certified Cloud Security
Professional - All Domains
Anything-as-a-Service >>>>Anything-as-a-service, or "XaaS," refers to the growing
diversity of services available over the Internet via cloud computing as opp
...
CCSP - Certified Cloud Security
Professional - All Domains
Anything-as-a-Service >>>>Anything-as-a-service, or "XaaS," refers to the growing
diversity of services available over the Internet via cloud computing as opposed to being
provided locally, or on premises.
Apache CloudStack >>>>An open source cloud computing and Infrastructure as a
Service (IaaS) platform developed to help Infrastructure as a Service make creating,
deploying, and managing cloud services easier by providing a complete "stack" of
features and components for cloud environments.
Cloud Administrator >>>>This individual is typically responsible for the implementation,
monitoring, and maintenance of the cloud within the organization or on behalf of an
organization (acting as a third party).
Cloud App (Cloud Application) >>>>Short for cloud application, cloud app is the phrase
used to describe a software application that is never installed on a local computer.
Instead, it is accessed via the Internet.
Cloud Application Architect >>>>Typically responsible for adapting, porting, or
deploying an application to a target cloud environment.
Cloud Application Management for Platforms (CAMP) >>>>A specification designed to
ease management of applications — including packaging and deployment — across
public and private cloud computing platforms.
Cloud Architect >>>>He or she will determine when and how a private cloud meets the
policies and needs of an organization's strategic goals and contractual requirements
(from a technical perspective).
Cloud Backup Service Provider >>>>A third-party entity that manages and distributes
remote, cloud-based data backup services and solutions to customers from a central
data center.
Cloud Backup Solutions >>>>Enable enterprises or individuals to store their data and
computer files on the Internet using a storage service provider rather than storing the
data locally on a physical disk, such as a hard drive or tape backup.
Cloud Computing >>>>A type of computing, comparable to grid computing that relies on
sharing computing resources rather than having local servers or personal devices to
handle applications.
Cloud Computing Accounting Software >>>>Accounting software that is hosted on
remote servers.Cloud Computing Reseller >>>>A company that purchases hosting services from a
cloud server hosting or cloud computing provider and then re-sells them to its own
customers.
Cloud Database >>>>A database accessible to clients from the cloud and delivered to
users on demand via the Internet.
Cloud Data Architect >>>>Ensures the various storage types and mechanisms utilized
within the cloud environment meet and conform to the relevant SLAs and that the
storage components are functioning according to their specified requirements.
Cloud Developer >>>>Focuses on development for the cloud infrastructure itself. This
role can vary from client tools or solutions engagements, through to systems
components.
Cloud Enablement >>>>The process of making available one or more of the following
services and infrastructures to create a public cloud-computing environment: cloud
provider, client, and application.
Cloud Management >>>>Software and technologies designed for operating and
monitoring the applications, data, and services residing in the cloud. Cloud
management tools help to ensure a company's cloud computing-based resources are
working optimally and properly interacting with users and other services.
Cloud Migration >>>>The process of transitioning all or part of a company's data,
applications, and services from on-site premises behind the firewall to the cloud, where
the information can be provided over the Internet on an on-demand basis.
Cloud OS >>>>A phrase frequently used in place of Platform as a Service (PaaS) to
denote an association to cloud computing.
Cloud Portability >>>>The ability to move applications and its associated data between
one cloud provider and another — or between public and private cloud environments.
Cloud Provider >>>>A service provider who offers customers storage or software
solutions available via a public network, usually the Internet.
Cloud Provisioning >>>>The deployment of a company's cloud computing strategy,
which typically first involves selecting which applications and services will reside in the
public cloud and which will remain on-site behind the firewall or in the private cloud.
Cloud Server Hosting >>>>A type of hosting in which hosting services are made
available to customers on demand via the Internet. Rather than being provided by a
single server or virtual server, cloud server hosting services are provided by multiple
connected servers that comprise a cloud.Cloud Services Broker (CSB) >>>>Typically a third-party entity or company that looks to
extend or enhance value to multiple customers of cloud-based services through
relationships with multiple cloud service providers.
Cloud Storage >>>>The storage of data online in the cloud, wherein a company's data
is stored in and accessible from multiple distributed and connected resources that
comprise a cloud.
Cloud Testing >>>>Load and performance testing conducted on the applications and
services provided via cloud computing — particularly the capability to access these
services — in order to ensure optimal performance and scalability under a wide variety
of conditions.
Desktop-as-a-service >>>>A form of virtual desktop infrastructure (VDI) in which the
VDI is outsourced and handled by a third party.
Enterprise Application >>>>The term used to describe applications — or software —
that a business would use to assist the organization in solving enterprise problems.
Eucalyptus >>>>An open source cloud computing and Infrastructure as a Service (IaaS)
platform for enabling private clouds.
FIPS 140-2 >>>>Primary goal is to accredit and distinguish secure and well-architected
cryptographic modules produced by private sector vendors who seek to have their
solutions and services certified for use in regulated industries that collect, store,
transfer, or share data that is deemed to be "sensitive" but not classified.
Hybrid Cloud Storage >>>>A combination of public cloud storage and private cloud
storage where some critical data resides in the enterprise's private cloud while other
data is stored and accessible from a public cloud storage provider.
Mobile Cloud Storage >>>>A form of cloud storage that applies to storing an individual's
mobile device data in the cloud and providing the individual with access to the data from
anywhere.
NIST SP 800-53 >>>>Its primary goal and objective is to ensure that appropriate
security requirements and security controls are applied to all U.S. Federal Government
information and information management systems.
Online Backup >>>>Leverages the Internet and cloud computing to create an attractive
off-site storage solution with little hardware requirements for any business of any size.
Personal Cloud Storage >>>>A form of cloud storage that applies to storing an
individual's data in the cloud and providing the individual with access to the data from
anywhere.Platform as a Service (PaaS) >>>>A way for customers to rent hardware, operating
systems, storage, and network capacity over the Internet from a cloud service provider.
Private Cloud Project >>>>Enable their IT infrastructure to become more capable of
quickly adapting to continually evolving business needs and requirements.
Private Cloud Storage >>>>A form of cloud storage where the enterprise data and cloud
storage resources both reside within the enterprise's data center and behind the firewall.
Public Cloud Storage >>>>A form of cloud storage where the enterprise and storage
service provider are separate and the data is stored outside of the enterprise's data
center.
Software as a Service (SaaS) >>>>The capability provided to the consumer is to use
the provider's applications running on a cloud infrastructure2. The applications are
accessible from various client devices through either a thin client interface, such as a
web browser (e.g., web-based email), or a program interface. The consumer does not
manage or control the underlying cloud infrastructure including network, servers,
operating systems, storage, or even individual application capabilities, with the possible
exception of limited user-specific application configuration settings.
Storage Cloud >>>>The collection of multiple distributed and connected resources
responsible for storing and managing data online in the cloud.
TCI Reference Architecture >>>>A methodology and a set of tools that enables security
professionals to leverage a common set of solutions that fulfill their common needs to
be able to assess where their internal IT and their cloud providers are in terms of
security capabilities and to plan a roadmap to meet the security needs of their business.
Vendor Lock-in >>>>Highlights where a customer may be unable to leave, migrate, or
transfer to an alternate provider due to technical or non-technical constraints.
Vertical Cloud Computing >>>>The optimization of cloud computing and cloud services
for a particular vertical (e.g., a specific industry) or specific-use application.
Virtualization Technologies >>>>Enable cloud computing to become a real and scalable
service offering due to the savings, sharing, and allocations of resources across multiple
tenants and environments.
All-or-Nothing-Transform with Reed-Solomon (AONT-RS) >>>>Integrates the AONT
and erasure coding. This method first encrypts and transforms the information and the
encryption key into blocks in a way that the information cannot be recovered without
using all the blocks, and then it uses the IDA to split the blocks into m shares that are
distributed to different cloud storage services (the same as in SSMS).Anonymization >>>>The act of permanently and completely removing personal
identifiers from data, such as converting personally identifiable information (PII) into
aggregated data.
Bit Splitting >>>>Usually involves splitting up and storing encrypted information across
different cloud storage services.
Business Impact Analysis (BIA) >>>>An exercise that determines the impact of losing
the support of any resource to an organization, establishes the escalation of that loss
over time, identifies the minimum resources needed to recover, and prioritizes the
recovery of processes and supporting systems.
Control >>>>Acts as a mechanism to restrict a list of possible actions down to allowed
or permitted actions.
Crypto-shredding >>>>The process of deliberately destroying the encryption keys that
were used to encrypt the data originally.
Data Loss Prevention (DLP) >>>>Audit and prevent unauthorized data exfiltration.
Components (3). 1.Discovery and classification 2.Monitoring 3.Enforcement
Degaussing >>>>Using strong magnets for scrambling data on magnetic media such as
hard drives and tapes.
Digital Rights Management (DRM) >>>>Focuses on security and encryption to prevent
unauthorized copying limit distribution to only those who pay.
Encryption >>>>An overt secret writing technique that uses a bidirectional algorithm in
which humanly readable information (referred to as plaintext) is converted into humanly
unintelligible information (referred to as ciphertext).
Encryption Key >>>>A special mathematical code that allows encryption
hardware/software to encode and then decipher an encrypted message.
Enterprise DRM >>>>Integration plan designed by Digital Equipment Corp. to provide
an operation platform for multi-vendor environment.
Homomorphic Encryption >>>>Enables processing of encrypted data without the need
to decrypt the data. It allows the cloud customer to upload data to a cloud service
provider for processing without the requirement to decipher the data first.
Infrastructure as a Service (IaaS) >>>>A model that provides a complete infrastructure
(e.g. servers, internetworking devices) and allows companies to install software on
provisioned servers and control the configurations of all devices.Key Management >>>>The generation, storage, distribution, deletion, archiving, and
application of keys in accordance with a security policy.
Masking >>>>A weak form of confidentiality assurance that replaces the original
information with asterisks or X's.
Non-Repudiation >>>>The assurance that a specific author actually did create and send
a specific item to a specific recipient, and that it was successfully received. With
assurance of non-repudiation, the sender of the message cannot later credibly deny
having sent the message, nor can the recipient credibly claim not to have received it.
Obfuscation >>>>The convoluting of code to such a degree that even if the source code
is obtained, it is not easily decipherable.
Personal Data >>>>Any information relating to an identified or identifiable natural
person data subject; an identifiable person is one who can be identified, directly or
indirectly, in particular by reference to an identification number or to one or more factors
specific to his physical, physiological, mental, economic, cultural, or social identity.
Personally Identifiable Information (PII) >>>>Information that can be traced back to an
individual user, e.g. your name, postal address, or e-mail address. Personal user
preferences tracked by a Web site via a cookie is also considered personally identifiable
when linked to other personally identifiable information provided by you online.
Record >>>>A data structure or collection of information that must be retained by an
organization for legal, regulatory or business reasons.
Service Level Agreement (SLA) >>>>A formal agreement between two or more
organizations: one that provides a service and the other the recipient of the service. It
may be a legal contract with incentives and penalties.
Tokenization >>>>The process of replacing sensitive data with unique identification
symbols that retain all the essential information about the data without compromising its
security.
Authentication >>>>The act of identifying or verifying the eligibility of a station,
originator, or individual to access specific categories of information. Typically, a
measure designed to protect against fraudulent transmissions by establishing the
validity of a transmission, message, station, or originator.
Authorization >>>>The granting of right of access to a user, program, or process.
Content Delivery Network (CDN) >>>>A service where data is replicated across the
global Internet.Corporate Governanc >>>>The relationship between the shareholders and other
stakeholders in the organization versus the senior management of the corporation.
Database as a Service >>>>In essence, a managed database service.
Demilitarized Zone (DMZ) >>>>Isolates network elements such as e-mail servers that,
because they can be accessed from trustless networks, are exposed to external
attacks.
Enterprise Risk Management >>>>The set of processes and structure to systematically
manage all risks to the enterprise.
Hardware Security Module (HSM) >>>>A device that can safely store and manage
encryption keys. This can be used in servers, data transmission, protecting log files, etc.
Management Plane >>>>Controls the entire infrastructure, and parts of it will be
exposed to customers independent of network location, it is a prime resource to protect.
Object Storage >>>>Objects (files) are stored with additional metadata (content type,
redundancy required, creation date, etc.). These objects are accessible through APIs
and potentially through a web user interface.
Redundant Array of Inexpensive Disks (RAID >>>>Instead of using one large disk to
store data, one can use many smaller disks (because they are cheaper).
An approach to using many low-cost drives as a group to improve performance, yet also
provides a degree of redundancy that makes the chance of data loss remote.
Security Alliance's Cloud Controls Matrix >>>>A framework to enable cooperation
between cloud consumers and cloud providers on demonstrating adequate risk
management
Software Defined Networking (SDN) >>>>A broad and developing concept addressing
the management of the various network components.
The objective is to provide a control plane to manage network traffic on a more abstract
level than through direct management of network components.
Application Normative Framework (ANF) >>>>A subset of the ONF that will contain only
the information required for a specific business application to reach the targeted level of
trust
Application Programming Interfaces (APIs) >>>>A set of routines, standards, protocols,
and tools for building software applications to access a Web-based software application
or Web tool
Application Virtualization >>>>Software technology that encapsulates application
software from the underlying operating system on which it is executedData Masking >>>>A method of creating a structurally similar but inauthentic version of
an organization's data that can be used for purposes such as software testing and user
training
Database Activity Monitoring (DAM) >>>>A database security technology for monitoring
and analyzing database activity that operates independently of the database
management system (DBMS) and does not rely on any form of native (DBMS-resident)
auditing or native logs such as trace or transaction logs
Dynamic Application Security Testing (DAST) >>>>The process of testing an
application or software product in an operating state
Federated Identity Management >>>>An arrangement that can be made among
multiple enterprises that lets subscribers use the same identification data to obtain
access to the networks of all enterprises in the group
Federated Single Sign-on (SSO) >>>>Single sign-on (SSO) systems allow a single user
authentication process across multiple IT systems or even organizations. SSO is a
subset of federated identity management, as it relates only to authentication and
technical interoperability
Identity and Access Management (IAM) >>>>The security discipline that enables the
right individuals to access the right resources at the right times for the right reasons
ISO/IEC 27034-1 >>>>Represents an overview of application security. It introduces
definitions, concepts, principles and processes involved in application security
Multi-factor Authentication >>>>A method of computer access control which a user can
pass by successfully presenting authentication factors from at least two of the three
categories: knowledge factors, such as passwords. Combines two or more independent
credentials: what the user knows, what the user has and what the user is.
Organizational Normative Framework (ONF) >>>>A framework of so-called containers
for all components of application security best practices catalogued and leveraged by
the organization
Quality of Service (QoS) >>>>Refers to the capability of a network to provide better
service to selected network traffic over various technologies, including Frame Relay,
Asynchronous Transfer Mode (ATM), Ethernet and 802.1 networks, SONET, and IProuted networks that may use any or all of these underlying technologies
Sandbox >>>>A testing environment that isolates untested code changes and outright
experimentation from the production environment or repository, in the context of
software development including Web development and revision controlSecurity Assertion Markup Language (SAML) >>>>A version of the SAML standard for
exchanging authentication and authorization data between security domains
Static Application Security Testing (SAST) >>>>A set of technologies designed to
analyze application source code, byte code and binaries for coding and design
conditions that are indicative of security vulnerabilities
STRIDE Threat Model >>>>Derived from an acronym for the following six threat
categories; Spoofing identity, Tampering with data, Repudiation, Information disclosure,
Denial of service, Elevation of privilege
Web Application Firewall (WAF) >>>>An appliance, server plugin, or filter that applies a
set of rules to an HTTP conversation. Generally, these rules cover common attacks
such as cross-site scripting (XSS) and SQL injection.
Community cloud >>>>This cloud infrastructure is provisioned for exclusive use by a
specific community of organizations with shared concerns (e.g., mission, security
requirements, policy, and compliance considerations).
Converged networking model >>>>Optimized for cloud deployments and utilizes
standard perimeter protection measures. The underlying storage and IP networks are
converged to maximize the benefits for a cloud workload.
Domain Name System (DNS) >>>>A hierarchical, distributed database that contains
mappings of DNS domain names to various types of data, such as Internet Protocol (IP)
addresses. DNS allows you to use friendly names, such as www.isc2.org, to easily
locate computers and other resources on a TCP/IP-based network.
Domain Name System Security Extensions (DNSSEC) >>>>A suite of extensions that
adds security to the Domain Name System (DNS) protocol by enabling DNS responses
to be validated. Specifically, DNSSEC provides origin authority, data integrity, and
authenticated denial of existence.
Honeypot >>>>Consists of a computer, data, or a network site that appears to be part of
a network, but is actually isolated and monitored, and which seems to contain
information or a resource of value to attackers.
Host Intrusion Detection Systems (HIDS) >>>>Monitors the inbound and outbound
packets from the device only and will alert the user or administrator if suspicious activity
is detected.
Hybrid cloud >>>>This cloud infrastructure is a composition of two or more distinct
cloud infrastructures (private, community, or public) that remain unique entities, but are
bound together by standardized or proprietary technology that enables data and
application portability (e.g., cloud bursting for load balancin
[Show More]