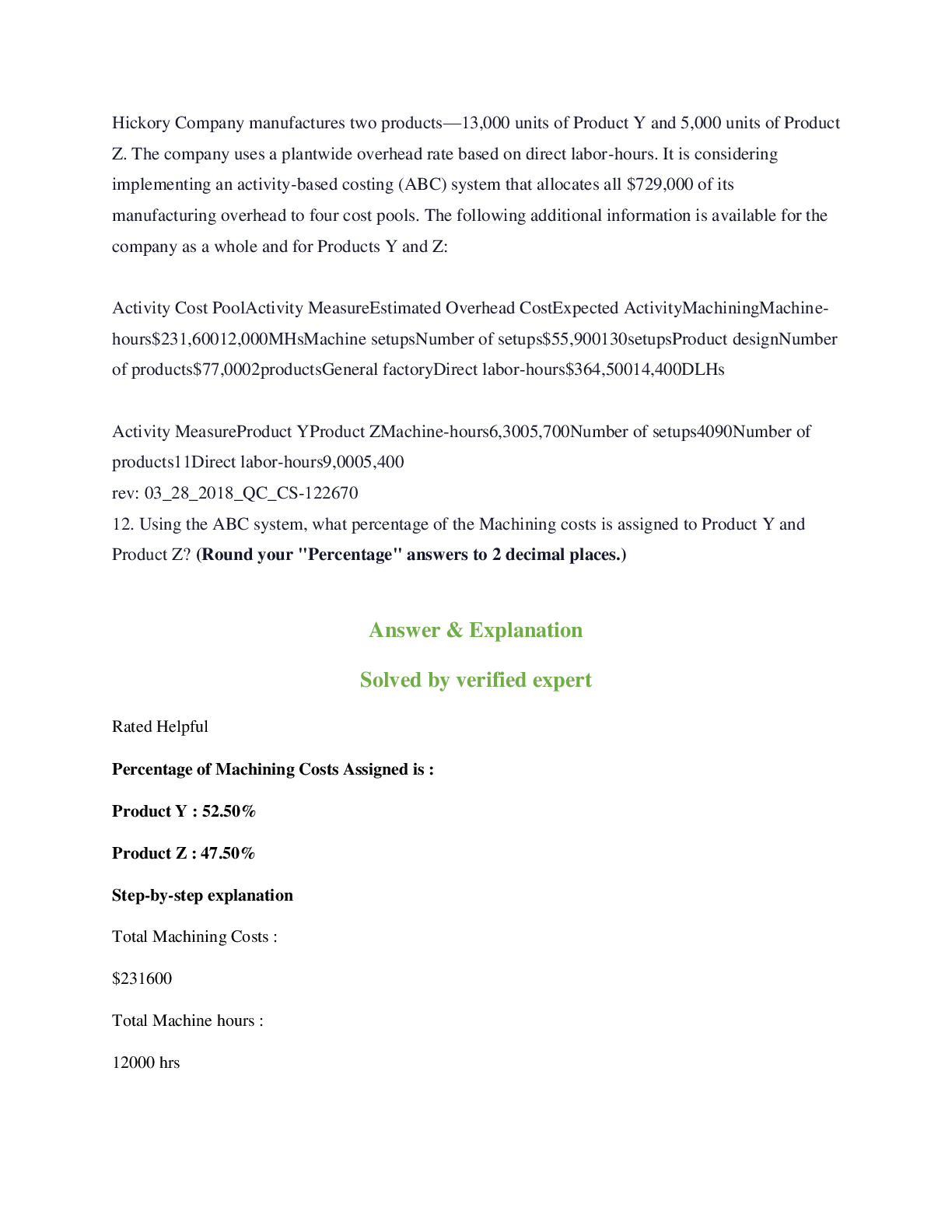
CompTIA Cybersecurity Analyst (CySA+) - Module 4:
Security Architecture and Tool Sets
Which framework was designed to widen the focus of an organization to overall
architecture?
COBIT
TOGAF
SABSA
ITIL -Answer- TOG
...
CompTIA Cybersecurity Analyst (CySA+) - Module 4:
Security Architecture and Tool Sets
Which framework was designed to widen the focus of an organization to overall
architecture?
COBIT
TOGAF
SABSA
ITIL -Answer- TOGAF (The Open Group Architecture Framework)
The procedures in place to test controls need to be examined only by internal parties to
ensure security.
True
False -Answer- False
Which policies are responsible for securing employee profiles?
Account Management Policy
Acceptable Use Policy
Data Ownership Policy
Password Policy -Answer- Account Management Policy & Password Policy
Which type of control would a software in charge of managing who has access to the
network be?
Administrative Control
Defined Parameters
Logical Control
Physical Control -Answer- Logical Control
Audits should be done by a third party to get a more accurate result.
True
False -Answer- True
What type of verification method is based on a judgement call?
Assessments
Audit
Evaluation
Certification -Answer- Evaluation
Which framework is distinguished by focusing exclusively on IT security?NIST
TOGAF
ISO
ITIL -Answer- NIST (National Institute of Standards and Technology)
What procedure is responsible for supplementing a lack of controls?
Patching
Managing Exceptions
Control Testing Procedures
Compensation Control Development -Answer- Compensation Control Development
Which policy might govern how guests may use the companies WiFi?
Data Retention Policy
Account Management Policy
Acceptable Use Policy
Data Ownership Policy -Answer- Acceptable Use Policy
A guideline is an adamant step by step listing of actions to be completed for a given
task.
True
False -Answer- False
In which procedure is everyone in the company told how to react and alert proper
members of staff?
Evidence Production
Continuous Monitoring
Remediation Plans
Managing Exceptions -Answer- Evidence Production
Which framework is distinguished by providing information assurance and is driven by
risk analysis?
TOGAF
ITIL
NIST
SABSA -Answer- SABSA (Sherwood Applied Business Security Architecture)
In which procedure do all factors need to be considered compared and tested before a
decision is made?
Managing ExceptionsRemediation Plans
Evidence Production
Continuous Monitoring -Answer- Remediation Plans
What are reasons that data should be retained past it's first use? (Choose Several)
Meeting legal and company policies
Keeping the data from being abused
Leverage
Backups for frequently changed files -Answer- Meeting legal and company policies &
Backups for frequently changed files
In which procedure are those involved given limited knowledge to develop from?
Evidence Production
Compensation Control
Testing Procedures
Managing Exceptions -Answer- Testing Procedures
An evaluation is scored against a benchmark or checklist.
True
False -Answer- False
Which procedure is typically put into place because it is virtually impossible to perfectly
match an entire environment?
Patching
Continuous Monitoring
Compensation Control
Managing Exceptions -Answer- Managing Exceptions
Which of these frameworks are commercial and must be purchased?
NIST
ISO
COBIT
SABSA -Answer- ISO (International Organization for Standardization) & COBIT (Control
Objectives for Information and Related Technologies)
The Data Ownership Policy includes both acquisition and destruction of data.
True
False -Answer- False
What policy determines how new users are provisioned/deprovisioned?Account Management Policy
Data Ownership Policy
Acceptable Use Policy
Password Policy -Answer- Account Management Policy
What assesses how well developed an organization's security capabilities are?
Audits
Remediation Plans
Maturity Model -Answer- Maturity Model
When attempting to provide defense in depth for personnel which of the following
controls can be put into place? Choose all that apply.
Dual Control
Scheduled Review
Training
Cryptography -Answer- Dual Control & Training
Network segmentation can be used in addition to security appliances in order to protect
a network.
True
False -Answer- True
Defense in depth is less of a necessity and more of a way for large companies who
have extra funds to better secure their network
True
False -Answer- False
Any singular technology can fail which leads to the necessity of defense in depth
True
False -Answer- True
Which part of continual improvement is implemented to address old processes that are
no longer efficient?
Scheduled Review
[Show More]