Information Technology > QUESTIONS & ANSWERS > IT Security: Defense against the digital dark arts Questions and Answers 100% Pass (All)
IT Security: Defense against the digital dark arts Questions and Answers 100% Pass
Document Content and Description Below
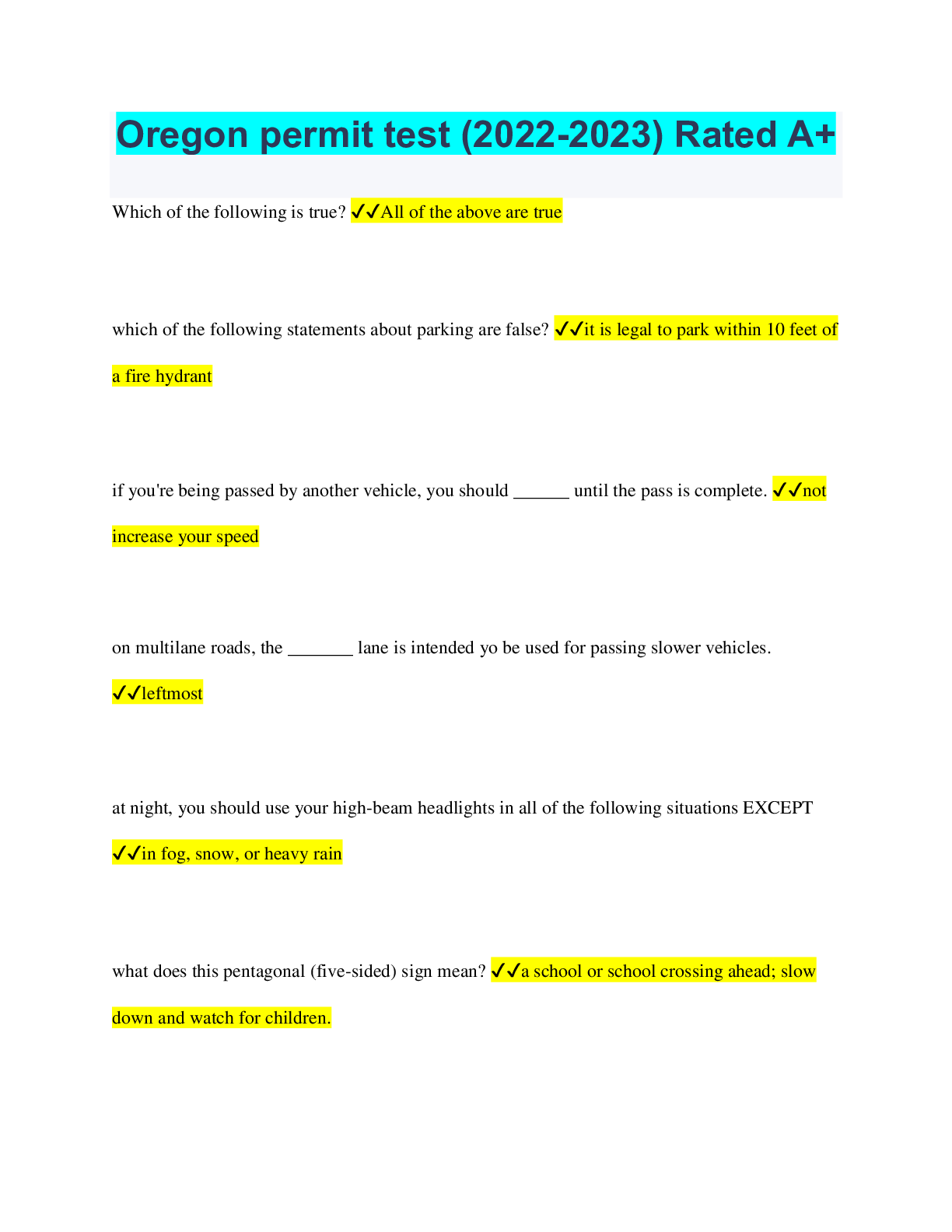
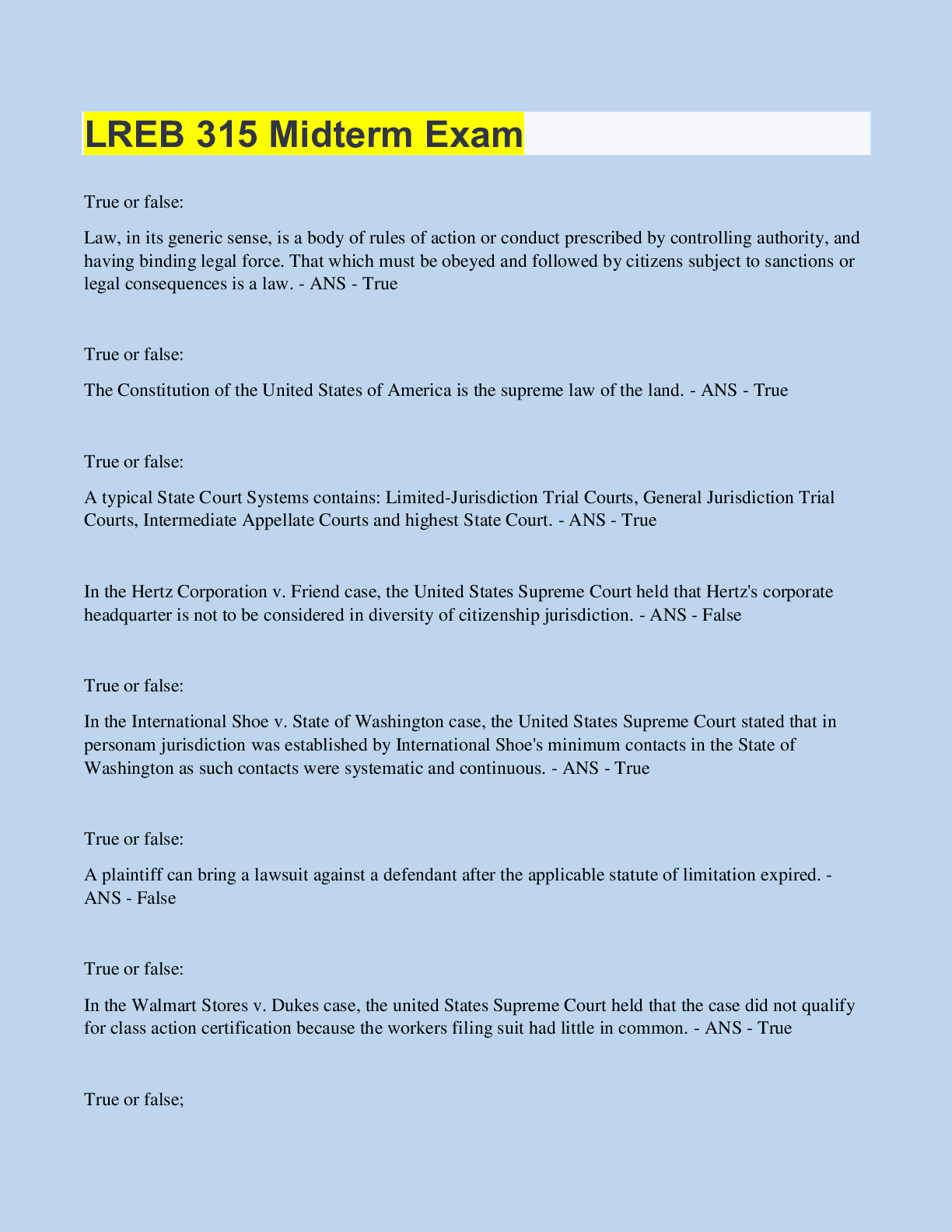
IT Security: Defense against the digital dark arts Questions and Answers 100% Pass Phishing, baiting, and tailgating are examples of ________ attacks. Malware Password Social engineering Networ... k ✔✔Social engineering An attacker could redirect your browser to a fake website login page using what kind of attack? Injection attack DNS cache poisoning attack DDoS attack SYN flood attack ✔✔DNS cache poisoning attack A(n) _____ attack is meant to prevent legitimate traffic from reaching a service. Injection Password Denial of Service DNS Cache poisoning ✔✔Denial of Service The best defense against password attacks is using strong _______. Firewall configs Passwords Encryption Antimalware software ✔✔Passwords Which of these is an example of the confidentiality principle that can help keep your data hidden from unwanted eyes? Preventing data loss Making sure the data hasn't been tampered with Preventing an unwanted download Protecting online accounts with password protection ✔✔Protecting online accounts with password protection Which of these is true of vulnerabilities? Check all that apply. A vulnerability is a flaw in the code of an application that can be exploited. An exploit is the possibility of taking advantage of a vulnerability bug in code. A vulnerability is the possibility of suffering a loss in the event of an attack. An exploit takes advantage of bugs and vulnerabilities. ✔✔A vulnerability is a flaw in the code of an application that can be exploited. An exploit takes advantage of bugs and vulnerabilities. Which of these is true of blackhat and whitehat hackers? Blackhats are malicious. Whitehats exploit weakness to help mitigate threats. Blackhats work with owners to fix problems. Whitehats are just trying to get into a system. Blackhats try to find weaknesses, but whitehats don't. Blackhats and whitehats shouldn't be trusted. ✔✔Blackhats are malicious. Whitehats exploit weakness to help mitigate threats. A hacker infected your computer to steal your Internet connection and used your machine's resources to mine Bitcoin. Wh [Show More]
Last updated: 2 years ago
Preview 1 out of 54 pages
.png)
Buy this document to get the full access instantly
Instant Download Access after purchase
Buy NowInstant download
We Accept:

Reviews( 0 )
$10.00
Can't find what you want? Try our AI powered Search
Document information
Connected school, study & course
About the document
Uploaded On
Oct 03, 2022
Number of pages
54
Written in
Additional information
This document has been written for:
Uploaded
Oct 03, 2022
Downloads
0
Views
110

.png)