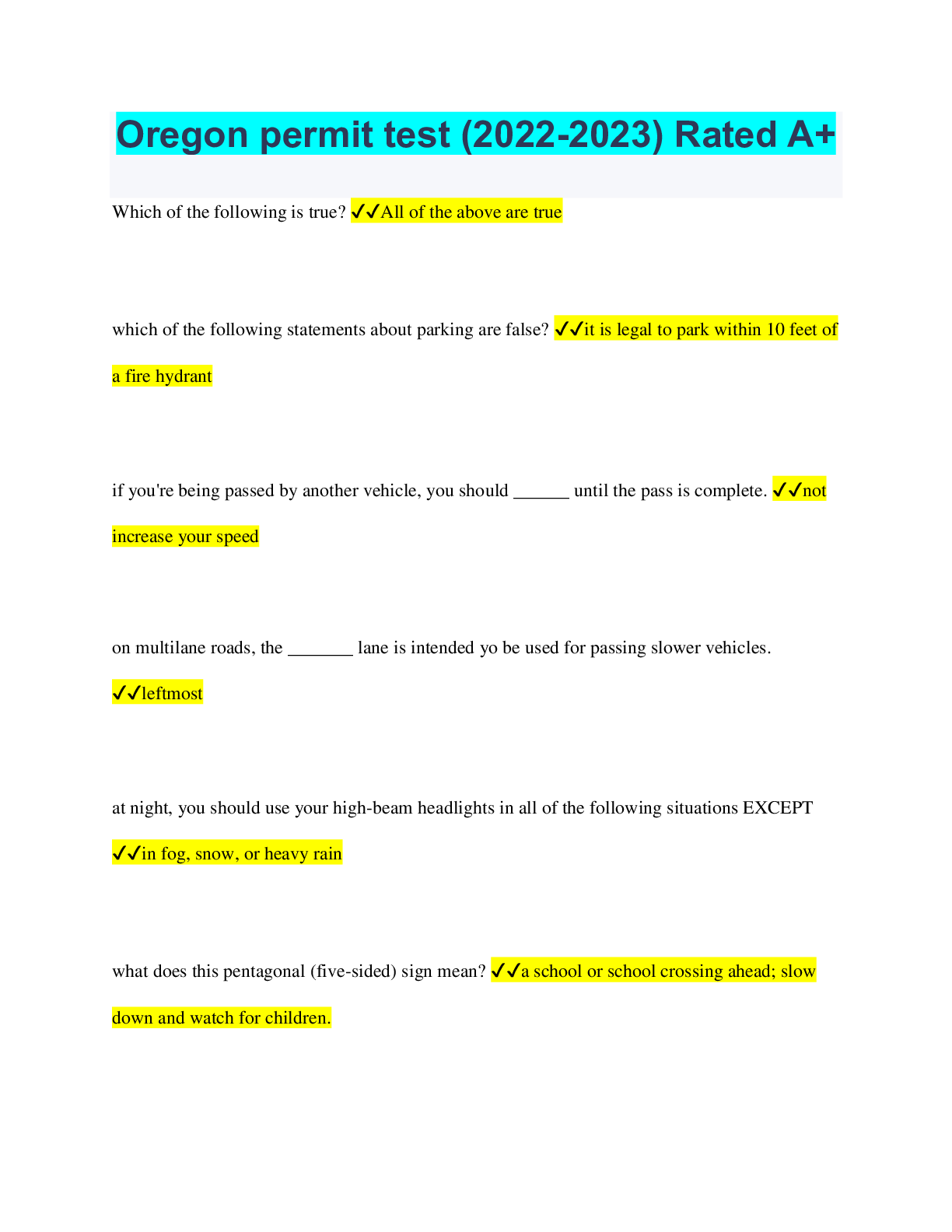
Information Technology > QUESTIONS & ANSWERS > IT Security: Defense against the digital dark arts questions and answers already passed (All)
IT Security: Defense against the digital dark arts questions and answers already passed
Document Content and Description Below
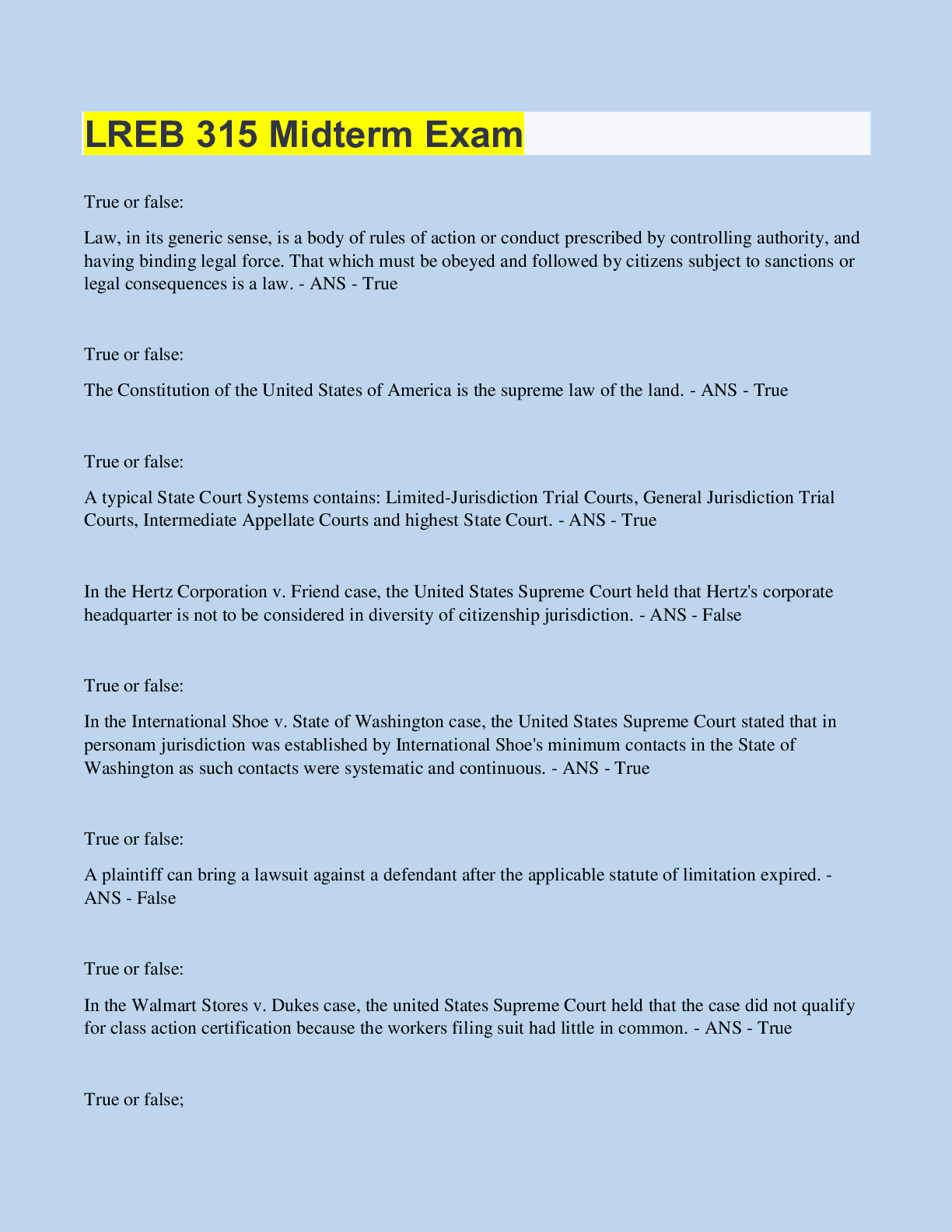
IT Security: Defense against the digital dark arts questions and answers already passed What information does a digital certificate contain? Check all that apply. ✔✔Digital signature Public Ke... y Data Identifying information of the certificate owner. A digital certificate contains the public key information, along with a digital signature from a CA. It also includes information about the certificate, like the entity that the certificate was issued to. Which type of encryption does SSL/TLS use? ✔✔Both : Asymmetric and Symmetric Encryptions What are some of the functions that a Trusted Platform Module can perform? Check all that apply. ✔✔Remote Attestation Data Binding and Sealing. A TPM can be used for remote attestation, ensuring that a host is a known good state and hasn't been modified or tampered (from a hardware and a software perspective). TPMs can also seal and bind data to them, encrypting data against the TPM. This also allows it to be decrypted by the TPM, only if the machine is in a good and trusted state. Plaintext is the original message, while _____ is the encrypted message. ✔✔Ciphertext The specific function of converting plaintext into ciphertext is called a(n) ______. ✔✔Encryption Algorithm Studying how often letters and pairs of letters occur in a language is referred to as _______. ✔✔Frequency Analysis. Frequency analysis involves studying how often letters occur, and looking for similarities in ciphertext to uncover possible plaintext mappings. True or false: The same plaintext encrypted using the same algorithm and same encryption key would result in different ciphertext outputs. ✔✔False. If the plaintext, algorithm, and key are all the same, the resulting ciphertext would also be the same. The practice of hiding messages instead of encoding them is referred to as ______. ✔✔Steganography ROT13 and a Caesar cipher are examples of _______. ✔✔Substitution Ciphers DES, RC4, and AES are examples of ______ encryption algorithms. ✔✔Symmetric Encryption Algorithm What are the two components of an asymmetric encryption system, necessary for encryption and decryption operations? Check all that apply. ✔✔Public key and Private Key In asymmetric encryption systems, there's a private key used for encryption, and a public key used for decryption. To create a public key signature, you would use the ______ key. ✔✔Private Key. The private key is used to sign data. This allows a third party to verify the signature using the public key, ensuring that the signature came from someone in possession of the private key. Using an asymmetric cryptosystem provides which of the following benefits? Check all that apply. ✔✔Non-repudiation Authenticity Confidentiality. Confidentiality is provided by the encryption, authenticity is achieved through the use of digital signatures, and non-repudiation is also provided by digitally signing data. If two different files result in the same hash, this is referred to as a ________. ✔✔Hash collision When authenticating a user's password, the password supplied by the user is authenticated by comparing the ____ of the password with the one stored on the system. ✔✔Hash. Passwords are verified by hashing and comparing hashes. This is to avoid storing plaintext passwords. If a rainbow table is used instead of brute-forcing hashes, what is the resource trade-off? ✔✔Rainbow tables use less computational resources and more storage space In a PKI system, what entity is responsible for issuing, storing, and signing certificates? ✔✔Certificate Authority. The certificate authority is the entity that signs, issues, and stores certificates. [Show More]
Last updated: 2 years ago
Preview 1 out of 3 pages
.png)
Buy this document to get the full access instantly
Instant Download Access after purchase
Buy NowInstant download
We Accept:

Reviews( 0 )
$7.00
Can't find what you want? Try our AI powered Search
Document information
Connected school, study & course
About the document
Uploaded On
Oct 03, 2022
Number of pages
3
Written in
Additional information
This document has been written for:
Uploaded
Oct 03, 2022
Downloads
0
Views
203

.png)